HAFNIUM targeting Exchange Servers with 0-day exploits
Important Exchange Update 03.03.2021 for all Microsoft Exchange Versions
Affected Exchange Version: 2010, 2013, 2013, 2016, 2019
12.03.2021
We have seen so many installations fail on certain blogs and forums. Please make sure understand the update process of patching a special Server like Exchange or SQL-Server. You never patch such system core server application without prior reading a few things.
There is absolute no business justification for an outage in the E-Mail system because someone wanted to patch a leak within a few minutes. Microsoft does its best to put some logic in the patch files. However they are just windows MSP files and the main logic for that is in the Windows installer Module which is on every server or client from MS.
10.03.2021
MS has to build/redo/re-tune their Exchange Repair TechNet/MSDN stuff due the high outage of Exchange on premise. Mostly related to non Exchange Groupware Engineer patching complex Exchange Servers in the emergency.
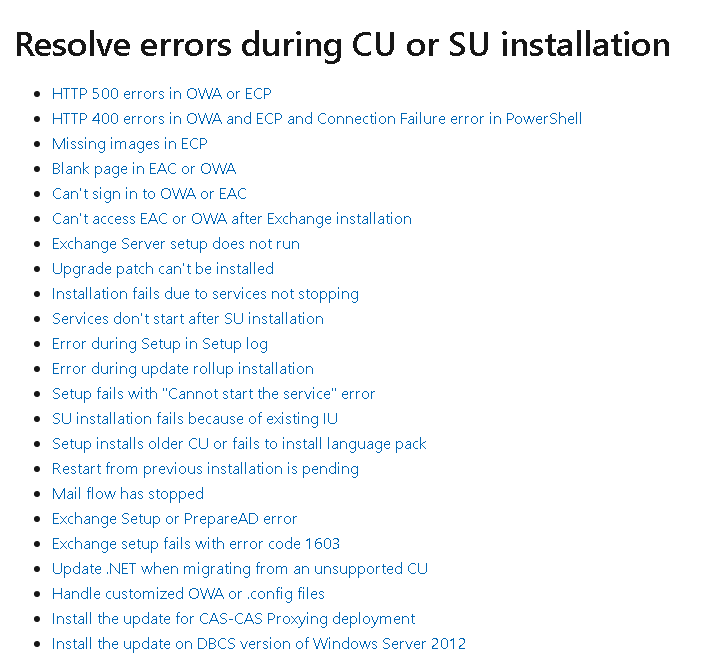
Repair failed installations of Exchange Cumulative and Security updates – Exchange | Microsoft Docs
REMINDER: Install any Exchange ROLLUP/ROLLUP with elevated Administrator rights!
-
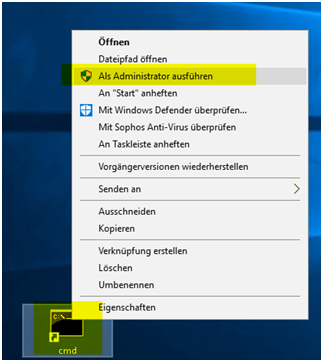
Select Start, and then type cmd.
-
Right-click Command Prompt from the search results, and then select Run as administrator.
-
If the User Account Control window appears, select the option to open an elevated Command Prompt window, and then select Continue. If the UAC window doesn’t appear, continue to the next step.
-
Type the full path of the .msp file for the security update, and then press Enter.
-
After the update installs, restart the server.

REMINDER: Make sure you have SCHEMA ADMIN rights for certain updates (Do not update with least privilege account like admin.butsch or 1stlevelsupportuser1 and if you do pre-heck it has all rights it needs
REMINDER:
Most of the modern ROLLUP for Exchange does a) Saves the config to many XML files b) does a complete uninstall of the full EXCHANGE d) Re-installs the full exchange with the settings from XML File (Do no interrupt, Wait until it’s done!) If you fail you will see Service deactivated and Exchange missing!
in larger Enterprise and PROXY environments
Always make sure that you:
*That the Exchange Server computer has access too all CRT Cert Revocation List address and also Network protocol related to CERTIFICATES (The computer when locked down MUST have access to WAN for these files)
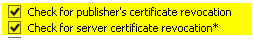
* You DISABLE Cert revocation in Internet Explorer 10/11 or EDGE on the Server (The computer account uses those settings for PROXY or CERT Revocation settings.
* DO disable Temporary cmd.exe > iexplore.exe > Advanced “Check for Server Certi*” < uncheck both and restart Exchange Setup for the ROLLUP/CU
Check CERT revocation from Exchange to WAN: If it’s not open HIT the Security Engineer in your company who closed internet access for Server and did not understand Cert Revocation. Never lock down Servers if you don’t understand what they do fully.
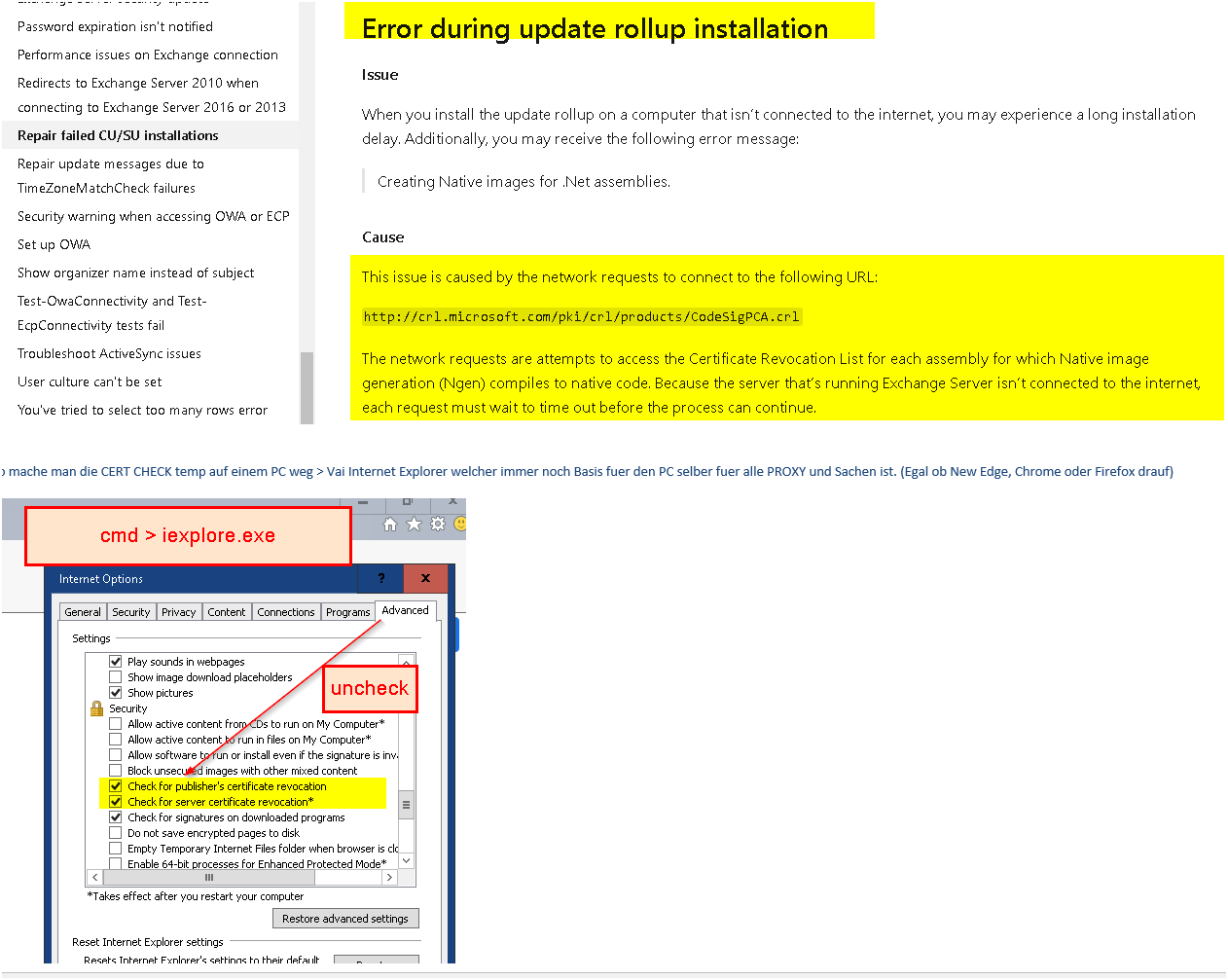
Microsoft explained with a graph now also since 25% did not understand at first glance. Including everyone I know.

Tech Links from 09.03.2011:
https://www.reddit.com/r/sysadmin/comments/m0d98h/exchange_nuked_and_reinstalled_what_can_i_and/
https://blueteamblog.com/microsoft-exchange-zero-days-mitigations-and-detections
News coverage done wrong:
Looks like the mainstream security magazines got something wrong here 😉 The patch was releases almost same time as the one from 2013/2016/2019. 2010 was supported and patched last week with a one shot patch already .

CVE we talk about:
CVE-2021-26854
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065, CVE-2021-27078.
CVE-2021-26855
Iis a server-side request forgery (SSRF) vulnerability in Exchange which allowed the attacker to send arbitrary HTTP requests and authenticate as the Exchange server.
CVE-2021-26857
Is an insecure deserialization vulnerability in the Unified Messaging service. Insecure deserialization is where untrusted user-controllable data is deserialized by a program. Exploiting this vulnerability gave HAFNIUM the ability to run code as SYSTEM on the Exchange server. This requires administrator permission or another vulnerability to exploit.
CVE-2021-26858
Is a post-authentication arbitrary file write vulnerability in Exchange. If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. They could authenticate by exploiting the CVE-2021-26855 SSRF vulnerability or by compromising a legitimate admin’s credentials.
CVE-2021-27065
Is a post-authentication arbitrary file write vulnerability in Exchange. If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. They could authenticate by exploiting the CVE-2021-26855 SSRF vulnerability or by compromising a legitimate admin’s credentials.
Here is what we talk about:
https://nvd.nist.gov/vuln/detail/CVE-2021-26854
https://www.microsoft.com/security/blog/2021/03/02/hafnium-targeting-exchange-servers/
Microsoft Made it a little bit complicated today. Here is maybe some help. They adapted their Blogs and documents during the day. First answer to the early links where asking where the patches are they mentioned.
So hopefully this information will help you to get your Exchange on premise safe soon.
To see what version you have use this Powershell commands:
Get-ExchangeServer | Format-List Name,Edition,AdminDisplayVersion
Invoke-Command -ScriptBlock {Get-Command Exsetup.exe | ForEach-Object {$_.FileversionInfo}}
Exchange Version overview:
Exchange Server – Buildnummern und Veröffentlichungstermine | Microsoft Docs
You then see following infos:
ProductVersion FileVersion FileName
14.03.0513.000 14.03.0513.000 D:\Program Files\Microsoft\Exchange Server\V14\bin\ExSetup.exe
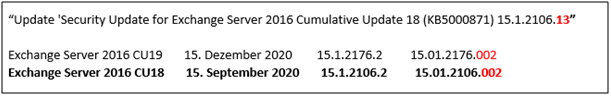
This changed AFTER the patch KB5000871 which makes certain Exchange version safe. See the15.1.2106.13. That is the Exchange 2016 CU 18 we patched with the KB5000871.
Screenshot: Sample shows a customer having Exchange 2016 RU 18 (Not already on 19 [Not needed to be safe]) 15.01.2106.002 and we made him safe with the Patch .13. (Lower Line)
IMPORTANT and CONFUSING:
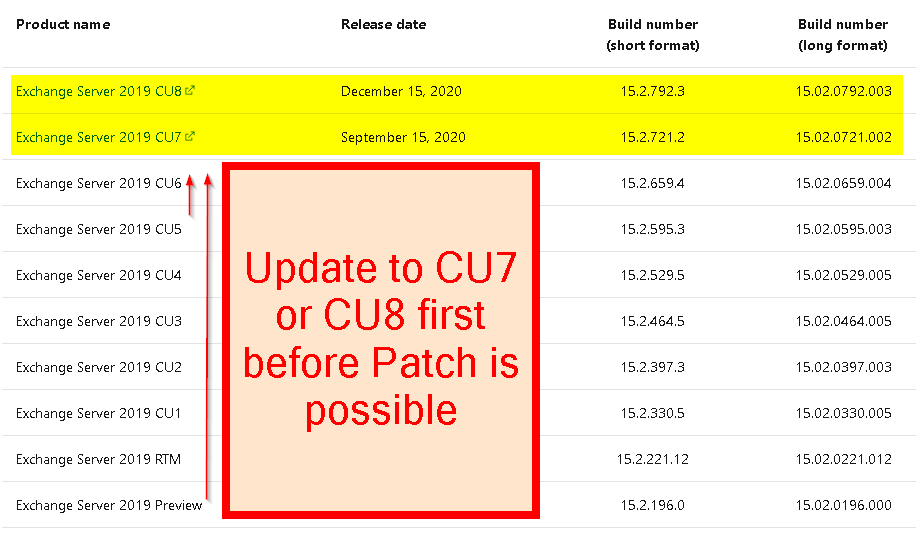
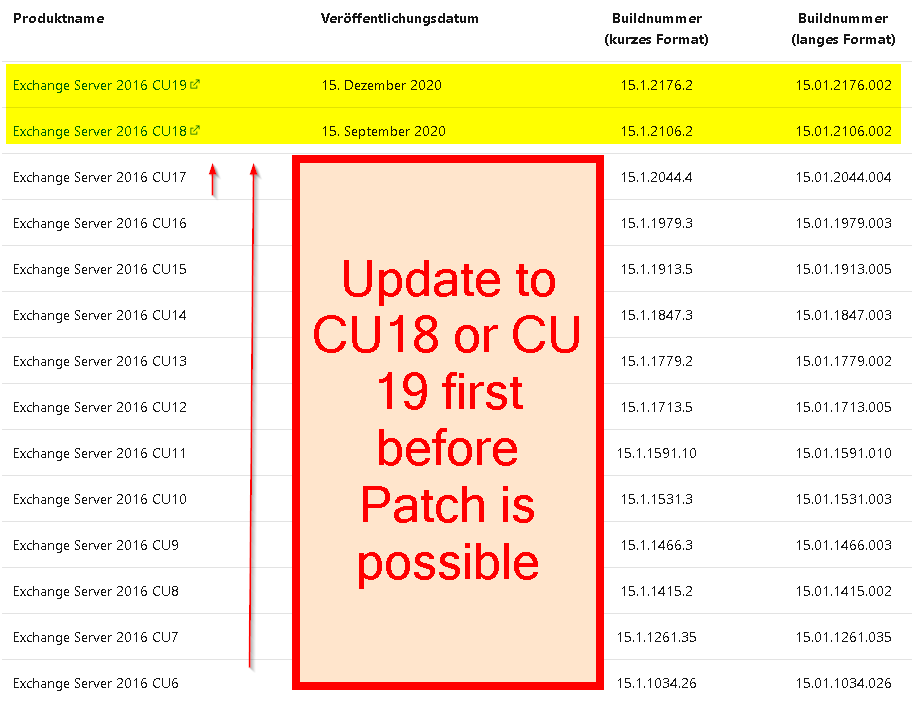
You have to be on a certain Patch level (Not the latest) before you can apply the Hot fix which makes you safe.
- On 2016 and the 2019 the last two regular versions
- On 2010 and 2013 the last version which was released
These versions you can patch with the Hotfix/Security Update for Exchange Server KB5000871
Exchange 2019 you minimum need 2019 CU7 (If you are not on CU7 first update to min CU7).
You don’t have to update to CU8 to be safe! Just install the KB5000871 for your correct version.
Exchange Server 2019 CU8 December 15, 2020 15.2.792.3 15.02.0792.003
https://www.microsoft.com/en-us/download/details.aspx?id=102770 (KB5000871 Download link)
Exchange Server 2019 CU7 September 15, 2020 15.2.721.2 15.02.0721.002
https://www.microsoft.com/en-us/download/details.aspx?id=102771 (KB5000871 Download link)
If your are not CU7 or CU8 then install one of those first and then the KB5000871 afterwards to be safe.
Check if you need Enterprise Admin/Schema Admin to install CU7 and CU8 (Don’t install with delegated Admin accounts!)
Reminder: Most of the modern ROLLUP for Exchange does a) Saves the config to many XML files b) does a complete uninstall of the full EXCHANGE d) Re-installs the full exchange with the settings from XML File (Do no interrupt, Wait until it’s done!) If you fail you will see Service deactivated and Exchange missing!
Exchange 2016 you Minimum need 2016 CU18 (If you are not on CU18 first update to min CU18).
You don’t have to update to CU19 to be safe! Just install the KB5000871 for your correct version.
Exchange Server 2016 CU19 15. Dezember 2020 15.1.2176.2 15.01.2176.002
https://www.microsoft.com/en-us/download/details.aspx?id=102772 (KB5000871 Download link)
Exchange Server 2016 CU18 15. September 2020 15.1.2106.2 15.01.2106.002
https://www.microsoft.com/en-us/download/details.aspx?id=102773 (KB5000871 Download link)
If your are not CU18 or CU19 then install one of those first and then the KB5000871 afterwards to be safe.
Both CU19 may make Active Directory Schema Updates so need be Domain Admin and Enterprise/Schema Admin! The patch can be installed with regular permission.
Reminder: Most of the modern ROLLUP for Exchange does a) Saves the config to many XML files b) does a complete uninstall of the full EXCHANGE d) Re-installs the full exchange with the settings from XML File (Do no interrupt, Wait until it’s done!) If you fail you will see Service deactivated and Exchange missing!
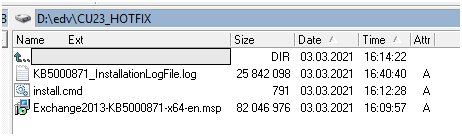
Exchange 2013 There is only one hot fix for the Patch which came out a year ago.
Exchange Server 2013 CU23 June 18, 2019 15.0.1497.2 15.00.1497.002
https://www.microsoft.com/en-us/download/details.aspx?id=102775 (KB5000871 Download link)
If you are not on 23 install the CU23 first and then the KB5000871 afterwards to be safe.
Reminder: Most of the modern ROLLUP for Exchange does a) Saves the config to many XML files b) does a complete uninstall of the d) Re-installs the full exchange with the settings from XML File (Do no interrupt, Wait until it’s done!)
Exchange 2010 There is new Rollup 32 free to all customers. Install the RU32 and you are good. That came out today and includes all you need.
Exchange Server 2010 SP3 Rollup 32 (Release today 03.03.2021 you can install without ESU)
https://www.microsoft.com/en-us/download/details.aspx?id=102774 (KB5000871 Download link)
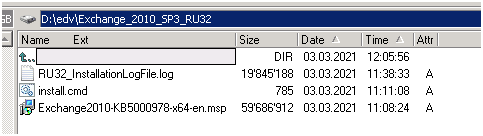
Install the MSP patch and the CU/ROLLUP the right way so you see more info.
* Check Execution Policy Powrshell angepasst? get-executionpolicy –list
* Check UAC OFF
* Run it elevated or it will not work
* Stop Schedule things like Backup, Snapshot from Netapp, Veeam Tasks maybe Antivirus Solution
* Make a link to cmd.exe on your Desktop and run that Elevated
* From that cmd.exe navigate to the Patch and run as example Exchange2016-KB5000871-x64-de.msp /lvx C:\KB5000871_InstallationLogFile.log
Or with a batch. Same thing it’s important that you install the Patch only elevated with run as Administrator.
:: ExchangeServer2016-x64-CU18_HOTFIX
:: V1.0, 03.03.2021, M. Butsch, First Release
:: ———————————————————————————————————————–
cls
@echo off
echo ACHTUNG auf GPO’s fuer Powershell oder UAC ACHTUNG
echo ———————————————————————–
echo – Execution Policy Powrshell angepasst? get-executionpolicy -list
echo – revoke Cert IE angepasst?
echo – UAC abgestellt
echo ———————————————————————–
pause
C:\edv\ExchangeServer2016-x64-CU18_HOTFIX\Exchange2016-KB5000871-x64-de.msp /lvx C:\edv\ExchangeServer2016-x64-CU18_HOTFIX\KB5000871_InstallationLogFile.log
pause

 Click on the Category button to get more articles regarding that product.
Click on the Category button to get more articles regarding that product.