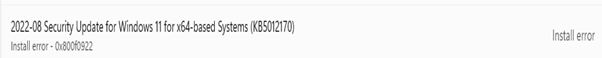
August 08/2022 Patch KB5012170 Update for Secure Boot DBX problem 0x800f0922
Problem: You can’t install August 2022 Update KB5012170 on some systems under certain condition where Secure Boot is enbled and not latest BIOS/UEFI Firmware . You will receive an Error 0x800f0922
Error: Package KB5015730 failed to be changed to the Installed state. Status: 0x800f0922.
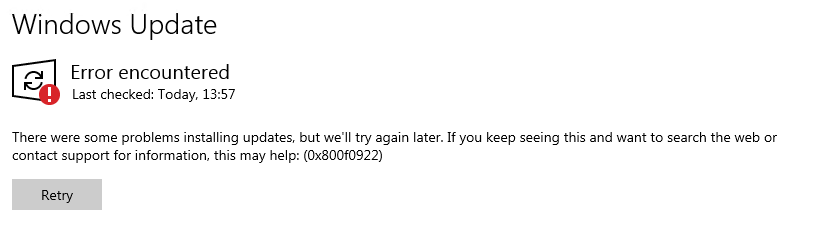
The patch does a revert
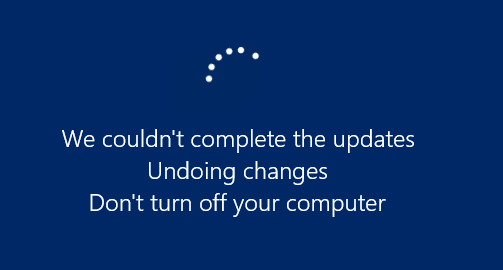
System which is not affected
The updates fixes some secure boot problems as example:
CVE-2022-34301 | Eurosoft Boot Loader Bypass
CVE-2022-34302 | New Horizon Data Systems Inc Boot Loader Bypass
CVE-2022-34303 | Crypto Pro Boot Loader Bypass
Microsoft main link:
KB5012170: Security update for Secure Boot DBX: August 9, 2022 (microsoft.com)
What does the KB describe:
Describes the problem that certain firmware/Bios and GPO Settings should not patch KB5012170. The KB is very hard to dunerstand. We try to help a little. Please keep in mind that you can’t update firmware without checking compatiblity on Laptops for docking station and maybe other things. In enterprise you can’t can’t just update laptop firmware over night and hope all is fine like microsoft thinks they can do with their M365/Azure solution and Autopolit clients. 😉
|
Keypoint / problem: |
|
If BitLocker Group Policy Configure TPM platform validation profile for native UEFI firmware configurations is enabled and PCR7 is selected by policy, it may result in the update failing to install. |
So what does that mean if you don’t have a post doc in IT?
Check if yout are affected with and have PCR7 active
You can find out the status of your UEFI / PCR7 / Bitlocker Setup with MSINFO32.exe (Elevated) or/and by running a DOS or PS command.
Some sample dumps and how to find out:
Affected product which has PCR7 mode shown:
Dell computer Precision 5530, Windows 10 21H2
msinfo32.exe commandline
shows:
Sicherer Startzustand Ein
PCR7-Konfiguration Gebunden
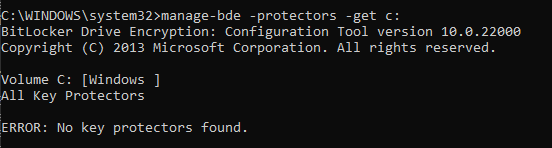
DOS: manage-bde -protectors -get c:
Shows:
Automate checking client for PCR7:
You may use a) Your software Deployment b) PSEXEC from systernals c) Do not use GPO to deploy software if you are not 100% fireproof with scripting
With psexec:
PsExec – Windows Sysinternals | Microsoft Docs
|
psexec -s \\computer001 c:\windows\system32\manage-bde.exe -protectors -get c: |
|
PsExec v2.4 – Execute processes remotely Copyright (C) 2001-2022 Mark Russinovich Sysinternals – www.sysinternals.com
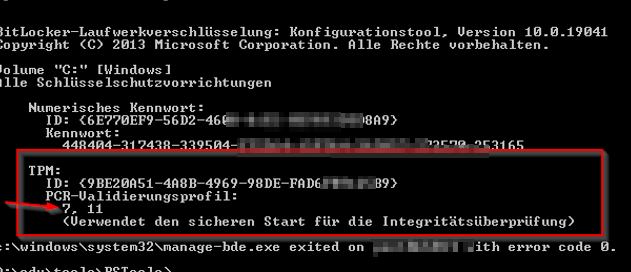
BitLocker-Laufwerkverschlüsselung: Konfigurationstool, Version 10.0.19041 Copyright (C) 2013 Microsoft Corporation. Alle Rechte vorbehalten.
Volume “C:” [Windows] Alle Schlüsselschutzvorrichtungen
Numerisches Kennwort: ID: {6E770EF9-56D2-430D-81SAFE82-0E9A555D3D8A9} Kennwort: 448404-317438-3449504-5442264-159SAFE764-262257-273570-253165
TPM: ID: {9BE23A51-4A8B-4649-98SAFEDE-FAD6FB7165B9} PCR-Validierungsprofil: 7, 11 (Verwendet den sicheren Start für die Integritätsüberprüfung)
c:\windows\system32\manage-bde.exe exited on pen10nb014 with error code 0. |
Auotmate the msinfo32.exe with psexec
psexec -s \\computer001 C:\windows\system32\msinfo32.exe /nfo c:\edv\00_report\computer.txt /report c:\edv\00_report\computer_re.txt
Description of Microsoft System Information (Msinfo32.exe) Tool
|
c:\edv\00_report\computer_re.txt |
|
Systeminformationsbericht erstellt am: 08/15/22 13:51:16 Systemname: SBBCARW10EL0145 [Systemübersicht]
Element Wert Betriebsystemname Microsoft Windows 10 Enterprise Version 10.0.19042 Build 19042 Weitere Betriebsystembeschreibung Nicht verfügbar Betriebsystemhersteller Microsoft Corporation Systemname PEN10NB014 Systemhersteller Dell Inc. Systemmodell Precision 5530 Systemtyp x64-basierter PC System-SKU 087D Prozessor Intel(R) Core(TM) i9-8950HK CPU @ 2.90GHz, 2904 MHz, 6 Kern(e), 12 logische(r) Prozessor(en) BIOS-Version/-Datum Dell Inc. 1.12.0, 27.06.2019 SMBIOS-Version 3.1 Version des eingebetteten Controllers 255.255 BIOS-Modus UEFI BaseBoard-Hersteller Dell Inc. BaseBoard-Produkt 0FP2W2 BaseBoard-Version A00 Plattformrolle Mobil Sicherer Startzustand Ein PCR7-Konfiguration Gebunden |
Other samples not affected:
An HP Elitedesk 800 G3 (Older) with a NON UEFI BIOS
Binding not possible becauee older machine and NOT UEFI BIOS (Legacy used) because of better Deployment OS reasons.
DOS: manage-bde -protectors -get c:
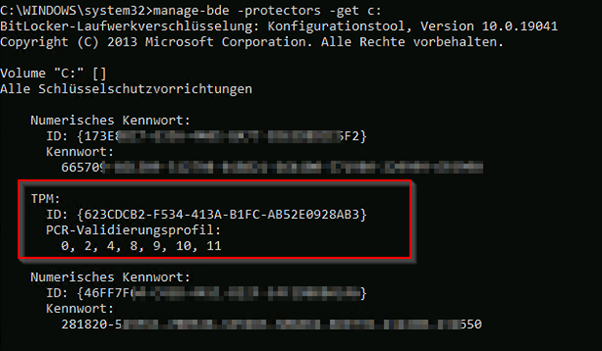
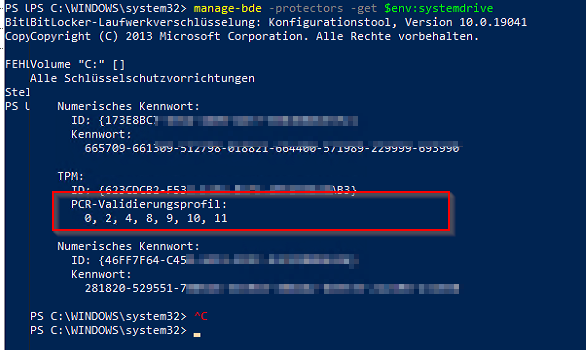
PS:
Msinfo32.exe
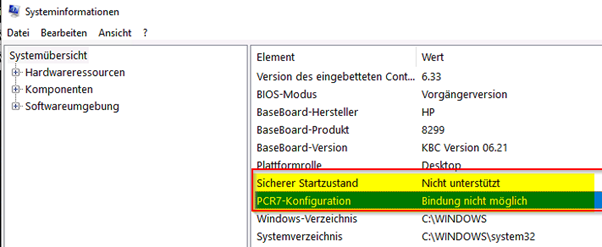
Some newer Home system from HP Elitedesk with UEFI no Bitlocker GO or Bitlocker active (Out of the box enduser system)
BINDING POSSIBLE
manage-bde -protectors -get c:
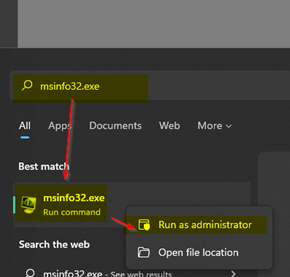
Below you see under PCR7 that you did NOT run msinfo32 under “Administrative/Elevated” it says “Elevation required to view”.
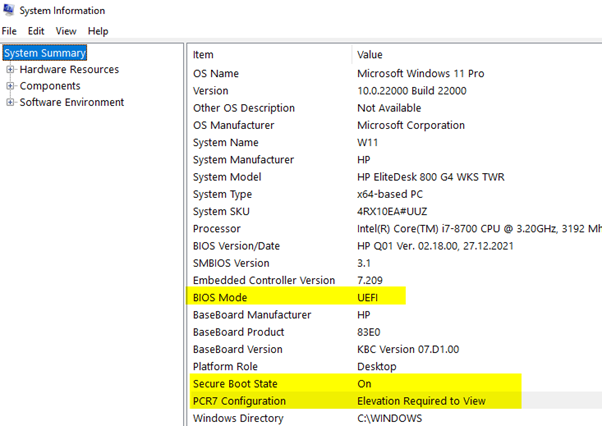
Here is msinfo32.exe with run as admin, PCR7 would be possible but is not activated
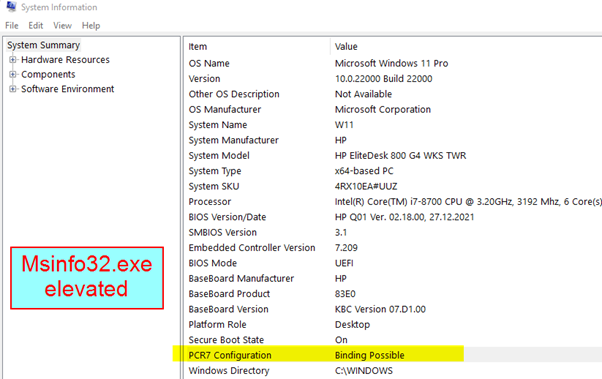
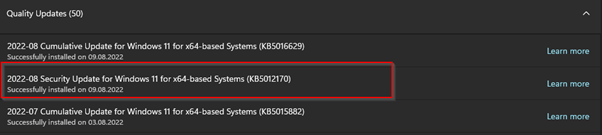
You can see in this specfic machine where PCR7 “Binding Possible” is shown there is not Bitlocker. That’s why withou the Fimrware Update which was offered by HP this was the patch has installed.
Solution
- Check that you have the latest Bios/Firmware
- Check if you have PCR7 enabled like mentioned above
If not possible > as example because your docking station is not comaptible with latest firmware
|
To workaround this issue, do one of the following before you deploy this update |
|
On a device that does not have Credential Gard enabled, run following command from an Administrator command prompt to suspend BitLocker for 1 restart cycle:
Manage-bde –Protectors –Disable C: -RebootCount 1
Then, deploy the update and restart the device to resume the BitLocker protection.
On a device that has Credential Guard enabled, run the following command from an Administrator command prompt to suspend BitLocker for 2 restart cycles:
Manage-bde –Protectors –Disable C: -RebootCount 3
Then, deploy the update and restart the device to resume the BitLocker protection. |
Some further links and infos regarding the path:
Troubleshoot the TPM (Windows) – Windows security | Microsoft Docs
R730xd, BitLocker, Secure Boot, PCR7 issue – Dell Community
|
Windows Server shows PCR7 configuration as “Binding not possible” – Windows Server | Microsoft Docs |
|
In this scenario, when you run msinfo32 to check the PCR7 Configuration, it’s displayed as Binding not possible. |
|
Windows Server shows PCR7 configuration as “Binding not possible” Article, 02/24/2022
This article introduces the Binding not possible issue in msinfo32 and the cause of the issue. This applies to both Windows clients and Windows Server.
PCR7 Configuration in msinfo32 Consider the following scenario:
Windows Server is installed on a secure boot-enabled platform. You enable Trusted Platform Module (TPM) 2.0 in Unified Extensible Firmware Interface (UEFI). You turn on BitLocker. You install chipset drivers and update the latest Microsoft Monthly Rollup. You also run tpm.msc to make sure that the TPM status is fine. The status displays The TPM is ready for use.
In this scenario, when you run msinfo32 to check the PCR7 Configuration, it’s displayed as Binding not possible. |

 Click on the Category button to get more articles regarding that product.
Click on the Category button to get more articles regarding that product.